Empowering modern networks with HPE Aruba 2930F Switch Series
The digital age demands higher connectivity and smoother data flow. You need a powerful and secure...
Navigating Cisco ISR Series for Enterprise Networks
In the fast-paced business world, companies constantly handle high-demand applications to keep...
SLAs: What are they and why are they important in aftermarket maintenance?
What is an SLA?
At its core, a service level agreement (SLA) is a formal document that outlines the...
NAS vs. SAN: Navigating Storage Options Simplified
The demand for data storage solutions has reached unprecedented new levels. Network-attached...
Understanding data destruction: Select techniques and partners
In the modern digital age, data is more valuable than ever before, and huge amounts of data comes...
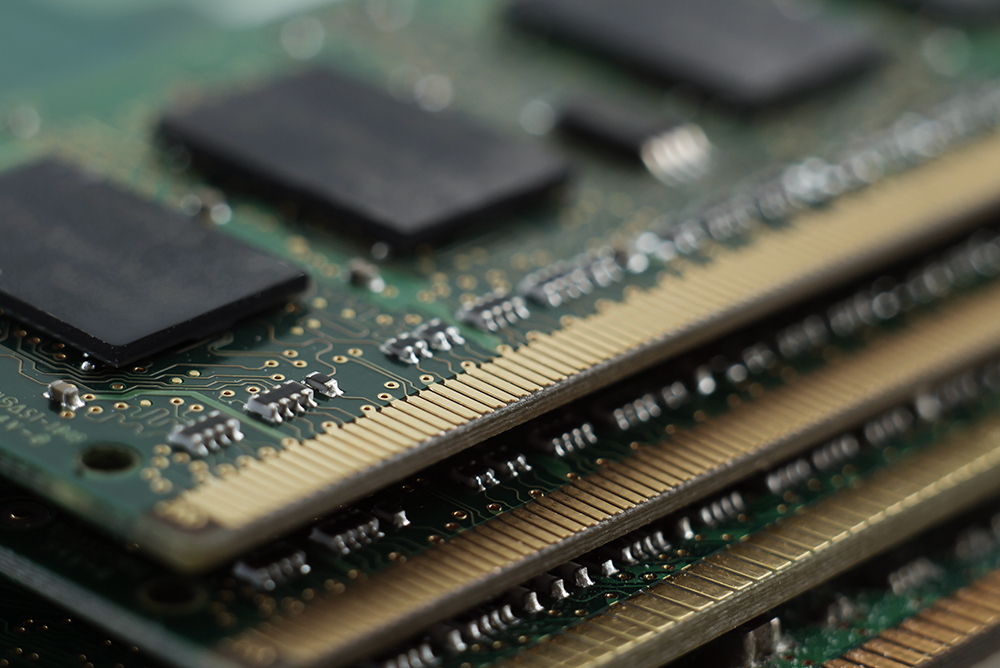
Server RAM: Different types, technologies and best practices
Enterprises try to strengthen their IT infrastructure by understanding the crucial role that...
Breaking down the Dell PowerEdge R-Series: Features and functions of R630, R640, R730, R740
Dell's PowerEdge R-series servers blend power and continuous performance, perfectly fitting the...
Layer 2 vs. Layer 3 switches: Optimizing your network infrastructure
Knowing the differences between Layer 2 and Layer 3 switches is essential while designing and...
Green Network: Environmental Benefits of Buying Refurbished Switches
In today’s digital age, smooth network connectivity is the cornerstone of successful operations....
Revolutionizing Data Centers: Impact of Reconditioned Servers on Scalability
A common saying in IT is, "If data is oil, then data centers are the new reservoirs." Data centers...
Recent Posts
The digital age demands higher connectivity and...
In the fast-paced business world, companies...
What is an SLA?
At its core, a service level...
Posts by Tag
- Server (18)
- Maintenance (17)
- Refurbished (15)
- IT Hardware (11)
- Switches (11)
- cisco (10)
- it assets (10)
- Refurbished Servers (8)
- Sustainability (8)
- Dell Server (7)
- hardware (7)
- Dell Equipment (5)
- IT Infrastructure (5)
- ITAD (5)
- network (5)
- Avaya (4)
- Hardware Failures (4)
- data center (4)
- microchip shortage (4)
- storage (4)
- supply chain (4)
- Cabling (3)
- E-Waste (3)
- HP (3)
- IT (3)
- IT Equipment (3)
- esg (3)
- Avaya Phones (2)
- HP switch (2)
- Hardware Security (2)
- IP Phones (2)
- NETWORKING (2)
- Server Maintenance (2)
- cisco router (2)
- decommissioning (2)
- factory reset (2)
- ucs (2)
- used cisco hardware (2)
- ACP (1)
- AP (1)
- Access Points (1)
- Aruba (1)
- Avay 9620 (1)
- Avaya 1608 (1)
- Avaya 4600 Series (1)
- Avaya 9600 Series (1)
- Avaya 9608 (1)
- Avaya DHCP (1)
- Brocade (1)
- Carbon Offsetting (1)
- Data Security (1)
- Fiber Optic Cables (1)
- Fiber Optic Cabling (1)
- Hybrid (1)
- IT Contributes (1)
- IT Network (1)
- IT Procurement Services (1)
- IT Vendor (1)
- POE (1)
- R2v3 (1)
- SLAs (1)
- Safeguard (1)
- Used Network Equipment (1)
- data destruction (1)
- strategy (1)
- urban mining (1)
- used cisco (1)
Popular Posts
When you are building a network that requires...
In efforts to provide an array of valuable...
When it comes to technology in our daily lives...